Apple’s Lockdown Mode: A Robust Barrier Against Sophisticated Spyware
As its debut nearly four years ago, Apple’s Lockdown Mode has demonstrated remarkable success in safeguarding devices from advanced spyware threats.The company confirms that no verified cases of device compromise have occured while this security feature was active, underscoring its critical role in defending users against highly targeted cyberattacks.
understanding Lockdown Mode: apple’s Shield Against Elite Spyware Threats
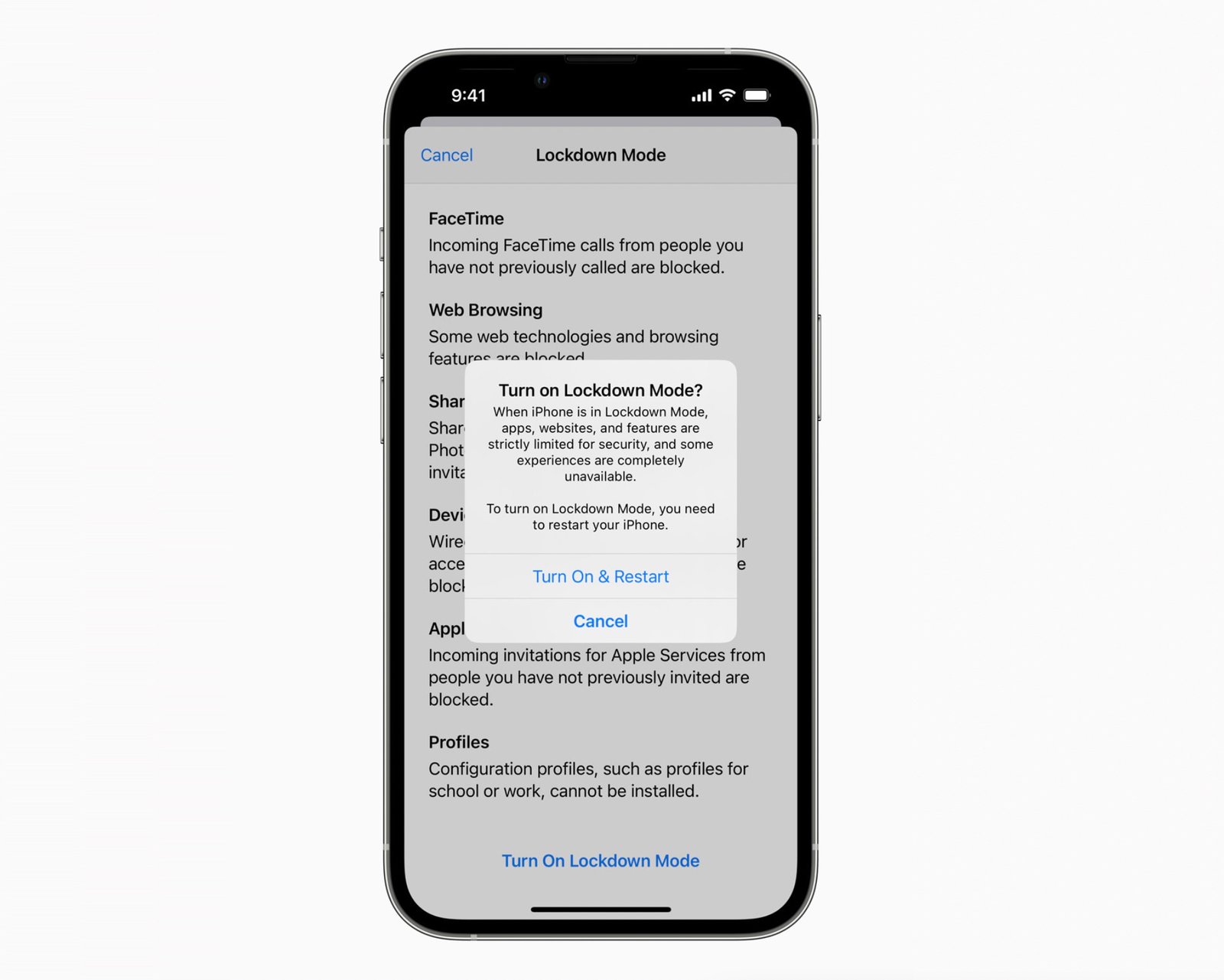
Introduced in 2022, Lockdown Mode is an optional security enhancement for iPhones and other Apple devices that disables specific functionalities commonly exploited by spyware developers. This defense mechanism primarily counters attacks from mercenary spyware firms such as NSO Group, Intellexa, and Paragon Solutions-entities notorious for supplying surveillance tools to governments worldwide.
The feature works by drastically limiting the potential entry points hackers can exploit. It blocks numerous attack vectors including message attachments and restricts certain web technologies like WebKit components-frequently enough leveraged in zero-click exploits where victims do not need to interact with their device for infection to occur.
Expert Insights Confirming Effectiveness
Donncha Ó Cearbhaill, head of Amnesty International’s Security Lab who has investigated global spyware incidents extensively, affirms there is no evidence of accomplished breaches on iPhones running Lockdown Mode during attempted intrusions. Similarly, Citizen Lab at the University of Toronto has documented multiple cases where this mode successfully thwarted infections from infamous spyware such as Pegasus (by NSO Group) and Predator (now under Intellexa).
“We have yet to see any iPhone compromised by mercenary spyware when Lockdown Mode was enabled,” Ó Cearbhaill states.
Further reinforcing these findings, Google researchers analyzing a potent iOS exploit kit observed that its malware would cease infection attempts if it detected Lockdown Mode was active-likely a strategy to avoid detection or failure during exploitation efforts.
The Expanding Scope of Spyware Detection on Apple Devices
Apple has significantly increased transparency regarding state-sponsored or mercenary spyware targeting its users. Notifications about potential compromises have been sent globally across more than 150 countries-a clear indication both of the widespread nature of these threats and Apple’s improved detection capabilities. Although exact figures remain confidential, cybersecurity experts estimate these alerts reach dozens or even hundreds annually among affected individuals worldwide.
The Technical Backbone: How Lockdown mode Fortifies Device Defenses
Cybersecurity analyst Patrick Wardle describes lockdown Mode as one of the most formidable consumer-level hardening features ever deployed on mobile platforms. By disabling entire categories of exploits related to messaging attachments and web content rendering engines like WebKit, it compels attackers to devise far more intricate-and expensive-methods for breaching devices.
“Lockdown Mode significantly diminishes remotely exploitable vulnerabilities,” Wardle explains. “It neutralizes many common delivery channels used in zero-click attacks.”
Navigating Usability trade-Offs While Maximizing Security Benefits
Activating Lockdown Mode can impact everyday user interactions-for exmaple requiring manual copying and pasting links instead of tapping them directly due to disabled link previews or attachment handling restrictions. Though these minor inconveniences sometimes trigger confusing notifications, digital security professionals widely recommend enabling this mode for anyone facing heightened risks from targeted cyberattacks or surveillance campaigns.
User Experiences Highlight Practical Advantages Despite Adjustments
A growing number of privacy advocates report consistently using Lockdown Mode without significant disruption beyond initial adaptation periods caused by disabled features. The reassurance gained through robust protection against sophisticated hacking attempts outweighs occasional usability quirks associated with this advanced security layer.





