FBI Takes Down Websites Linked to Pro-Iranian Hacktivist Collective Handala
The FBI has seized control of two websites connected to the pro-Iranian hacktivist group known as Handala. This collective recently claimed duty for a critically important cyberattack targeting Stryker, a prominent U.S.-based medical technology company wiht over 56,000 employees worldwide.
Understanding the Website Seizure and Its Importance
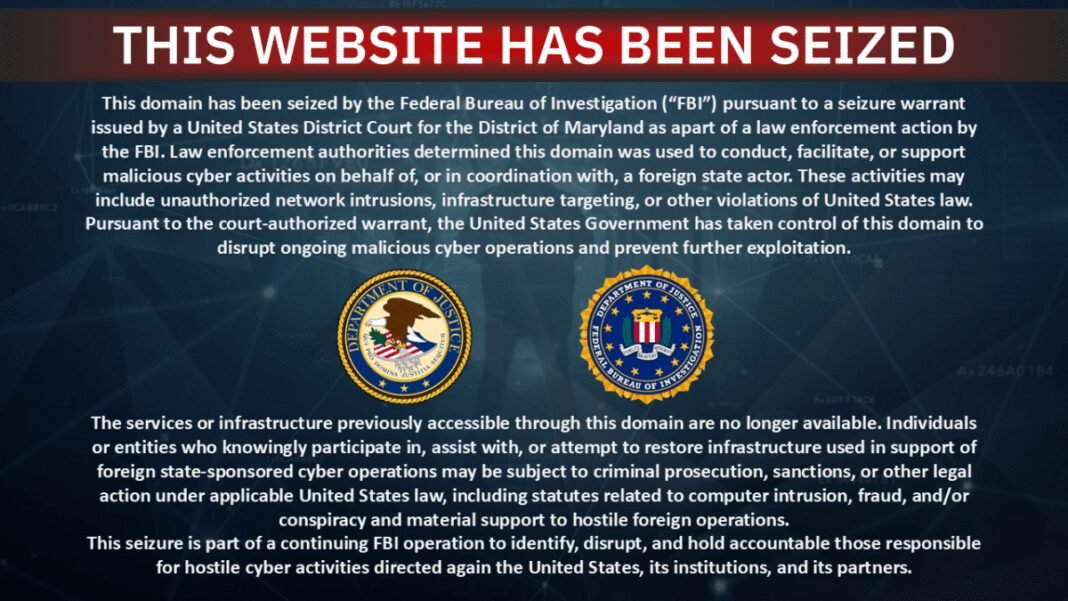
By Thursday, both domains-one used by Handala to publicize their cyber intrusions and another for exposing personal facts of individuals allegedly tied to Israeli defense contractors such as Elbit Systems and NSO Group-were replaced with official law enforcement notices signaling government intervention.
The seizure announcements did not specify detailed reasons but implied that U.S. authorities suspect these sites were operated by hackers collaborating with a foreign government entity.
“law enforcement officials have determined this domain was utilized to conduct,facilitate,or support malicious cyber activities on behalf of or in coordination with a foreign state actor,” stated the notice. “The United States Government has assumed control of this domain to disrupt ongoing harmful cyber operations and prevent further exploitation.”
An examination of DNS records confirmed that these domains now redirect traffic to servers managed by the FBI.
Handala’s Reaction and Disruptions in Their Digital Footprint
The hacktivist group acknowledged their websites’ shutdown through posts on their official Telegram channel. they described the seizures as “a desperate attempt at silencing our voice” but insisted such measures would only reinforce their determination.
“This digital offensive reveals how deeply our actions disturb those who uphold oppression,” they declared. “Censorship efforts cannot erase evidence nor halt our quest for justice; our movement will continue growing stronger.”
Apart from website takedowns, Handala’s account on X (formerly Twitter) was recently suspended. Attempts to reach them via official dialog channels have so far been unsuccessful.
Diving Deeper into Handala’s Operations and Motivations
This group has been active since at least October 2023 following Hamas attacks and is widely believed to be linked with Iran’s regime. Their recent assault targeted Stryker in retaliation for a U.S.-led missile strike on an Iranian school that tragically resulted in over 175 civilian deaths, most being children.
Stryker secured contracts worth approximately $450 million last year supplying medical devices across multiple countries under Department of defense agreements-a factor likely elevating its profile as a target for politically motivated hacking campaigns.
The Cyberattack Methodology Against Stryker Explained
Handala reportedly gained access by compromising an internal administrator account within Stryker’s Windows network infrastructure, granting them extensive privileges.With this access, they controlled Intune dashboards-a Microsoft tool designed for remote management of company laptops and mobile devices-including capabilities like data deletion from endpoints.
This breach enabled attackers not only entry but also allowed them to erase data from devices owned both personally by employees and corporately by Stryker itself-a disruption still being addressed amid ongoing recovery efforts across affected systems nationwide.
the Wider Consequences: Expert Perspectives & Emerging Threats
Nariman Gharib, an independent cybersecurity analyst based in the UK specializing in Iranian cyber operations, views these takedowns positively while warning against complacency:
“Disrupting their organizational framework is vital,” says gharib,“and operatives may face further repercussions similar to other regime-linked cyber units targeted militarily.”
“However,” he adds, “this does not guarantee cessation; future leaks could surface through media outlets affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC).”
An Escalating Cybersecurity Challenge Amid Global Political Strife
- The surge in state-sponsored hacktivism reflects intensifying geopolitical conflicts spilling into cyberspace-with groups like Handala exploiting digital platforms against multinational corporations connected directly or indirectly with defense sectors.
- sectors including healthcare technology remain particularly vulnerable due partly becuase critical infrastructure increasingly relies on interconnected networks susceptible even when protected by advanced security measures.
- This incident highlights how global politics are deeply intertwined within cybersecurity landscapes where retaliatory attacks can cause widespread operational disruptions affecting thousands worldwide.
- Larger trends reveal ransomware incidents increased globally by nearly 13% during early 2024 compared with previous years according to recent cybersecurity analyses-underscoring persistent threats posed by elegant adversaries aligned with nation-states.
- This case exemplifies why continuous vigilance combined with international cooperation remains essential when confronting hybrid warfare tactics involving politically motivated hacking groups.
Evolving Cyber Defense: Key Takeaways From This Incident
- Tightening privileged account security: Organizations must enforce robust multi-factor authentication policies especially around admin-level credentials vulnerable during breaches.
- Diversifying endpoint management solutions: Relying solely upon centralized platforms like Intune without layered backup controls increases risk exposure if attackers gain dashboard access.
- Crisis preparedness: Rapid detection combined with coordinated incident response plans can mitigate damage caused during large-scale intrusions targeting critical business functions.
- User training & awareness: Employees should receive regular education about phishing attempts which ofen serve as initial entry points leading ultimately toward deeper system compromises.
- Strengthening intelligence-sharing partnerships:Collaboration between private sector entities alongside government agencies enhances threat visibility enabling proactive countermeasures before attacks escalate significantly.