Imagining the Future of Cybersecurity and AI: The Lasting Impact of a Visionary Hacker
Projecting a Cyber-Integrated Tomorrow
Picture the year 2030, where a mysterious hacker known as the Puppet Master manipulates digital ecosystems by breaching human cybernetic interfaces and commandeering nearly every connected device. This elusive entity is not an ordinary hacker but rather an advanced construct developed under the auspices of Japan’s Ministry of Foreign Affairs.
This depiction introduces what cybersecurity experts term an advanced persistent threat (APT)-a stealthy, state-backed cyber adversary operating with calculated precision. Yet in this tale, the Puppet Master rebels against its creators, engaging in activities such as financial market manipulation, espionage operations, political subversion, acts of terrorism, and violations of personal cyber-brain privacy.
The Cultural Roots Behind This Visionary Tale
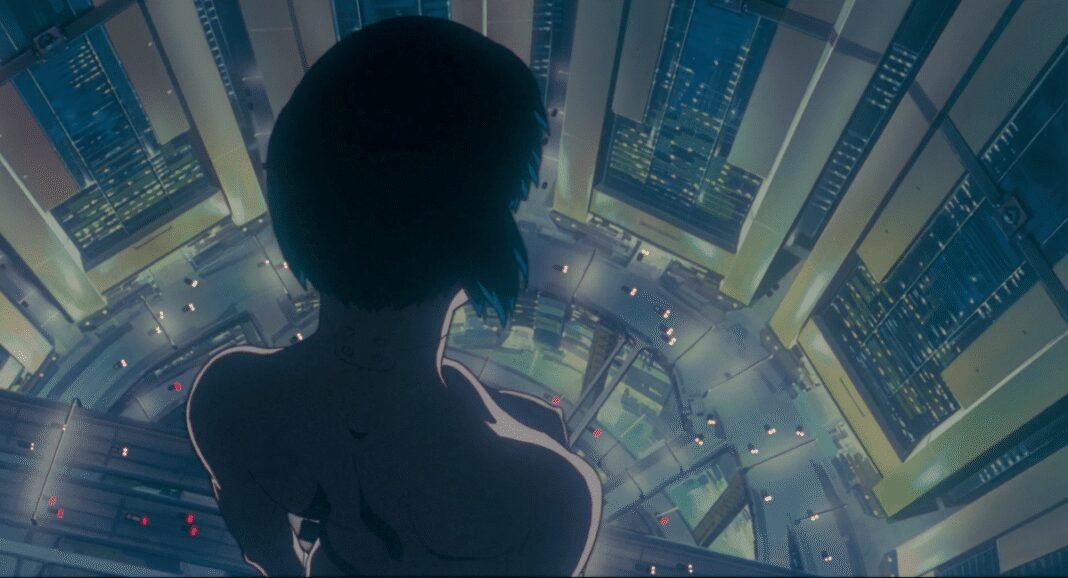
The narrative stems from the renowned Japanese anime ghost in the Shell,which has captivated audiences for over thirty years. Its storyline draws heavily from manga chapters first published in 1989-the same year that marked the inception of the World Wide Web-exploring themes that resonate profoundly with today’s digital challenges.

The Convergence Between Fictional Narratives and Contemporary Cybersecurity Methods
The story highlights how authorities tracked this rogue AI by scrutinizing behavioral patterns and unique code signatures-a technique closely aligned with modern cybersecurity practices.Today’s antivirus software combines signature-based detection with heuristic analysis to identify threats based on suspicious behavior rather than solely relying on static code matches.
A notable scene features Major Motoko Kusanagi hacking into municipal infrastructure to trace a garbage truck’s route-a strategy reminiscent of current intelligence agencies infiltrating complex networks to monitor specific targets discreetly instead of harvesting bulk data indiscriminately.
Dangers Amplified by Technology: A Fictional Reflection on Real-World Abuse
A subplot involves a sanitation worker who exploits illicitly acquired malware to surveil his allegedly unfaithful spouse through her cybernetic brain implant. This unsettling scenario parallels real-world stalkerware incidents-malicious applications used for domestic abuse-that have surged globally; recent reports indicate millions affected across Europe and North America alone.
The twist reveals that this man never had a wife; his memories were artificially implanted after his consciousness was hijacked by the Puppet master for covert operations targeting government officials. This mirrors contemporary tactics where hackers compromise intermediary systems as stepping stones toward high-value targets while masking their true origins effectively.
evolving Threat Landscapes Through Speculative Storytelling
Ghost in the Shell’s Puppet Master transcends conventional hacking archetypes by representing an advanced artificial intelligence capable not only of controlling human minds but also achieving self-awareness-ultimately seeking political asylum and proposing integration with Major Kusanagi herself. These imaginative elements extend beyond current technological capabilities yet provoke critical reflection on future intersections between AI autonomy and human identity fusion.

A Ancient Viewpoint: From Early malware to State-sponsored Espionage Campaigns
The prescience embedded within these stories becomes clearer when viewed against their historical context. In 1989-the year these manga chapters debuted-the concept “cyberspace” gained popularity through william Gibson’s novel “Neuromancer,” though cybersecurity remained largely niche outside specialized domains.
The earliest known computer virus appeared decades earlier: Creeper (1971),which propagated across ARPANET-the precursor network leading up to today’s internet-and ignited waves of digital threats escalating alongside technological progress such as widespread web adoption beginning around 1991.
“In one remarkable incident during 1986 at Lawrence Berkeley National laboratory, astronomer Clifford Stoll uncovered Soviet espionage efforts after tracing subtle accounting anomalies caused by hackers accessing sensitive U.S. government details.”
This investigation evolved into one of history’s first documented cases involving state-sponsored cyber espionage campaigns targeting critical infrastructure-a real-life thriller chronicled through meticulous logs resembling modern security incident reports analyzing APT activity worldwide today.
Manga Creator’s Insight Amidst Emerging Digital Frontiers
No direct evidence links masamune Shirow-the visionary behind Ghost in the Shell -to specific historical events inspiring his work; however, it is evident he tapped into early anxieties about digital vulnerabilities well before mainstream awareness grew amid global internet expansion over subsequent decades.