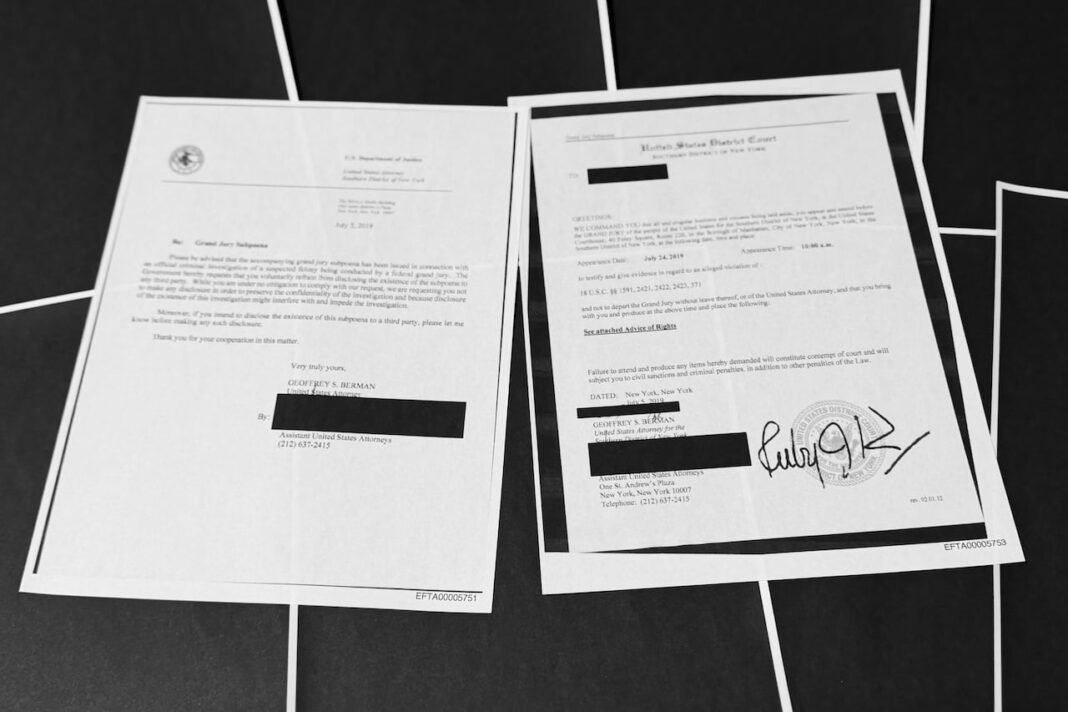
Uncovering Concealed Information in the Jeffrey Epstein Files
The recent disclosure of the Jeffrey Epstein files released by the U.S. Department of justice has reignited public scrutiny, largely due to extensive redactions that obscure critical details. While survivors, legal representatives, and numerous Democratic lawmakers have voiced frustration over thes heavily censored sections, digital investigators have developed innovative methods to expose some of the hidden content.
Exploiting digital Redaction Flaws to Reveal Hidden Text
A widely used technique involves selecting and copying blacked-out text from PDF documents and pasting it into a separate editor where concealed words become legible. This approach takes advantage of a common error in document redaction: instead of permanently removing sensitive information, redactions are often applied as visual masks layered over intact underlying text.
Experts in cybersecurity explain that this vulnerability occurs because many redaction tools only cover text visually without deleting it from the file’s data structure. As a result, although censored on screen or printouts, original content remains embedded and accessible through simple copy-paste actions.
Example From Online investigators’ Findings
User communities on platforms like Mastodon have shared detailed tutorials illustrating how they uncovered confidential passages by highlighting obscured sections and transferring them into word processors. one participant noted how effortlessly he retrieved sensitive excerpts using this method-raising concerns about how many other official documents might be similarly compromised.
Image Manipulation Techniques Expose More Than Expected
An alternative strategy employs photo editing software available on smartphones or computers to analyze scanned images with blacked-out areas. By tweaking brightness, contrast, exposure levels, or shadow intensity, users can sometimes detect faint imprints beneath digital ink blocks covering classified information.
This method has proven effective in several recent high-profile leaks involving court records and confidential reports where conventional digital extraction failed to yield results.
The Broader Implications for Public Awareness and Legal Cases
The newly revealed fragments shed light on Epstein’s modus operandi-detailing his exploitation tactics alongside intricate financial schemes designed to hide assets through shell corporations and trusts. For instance, recently surfaced exhibits from civil lawsuits filed in territories like the U.S. Virgin Islands outline accusations against estate managers allegedly complicit in sustaining abuse networks linked to Epstein’s operations.
No Definitive Links Between Epstein And Prominent Figures Yet found
Despite speculation fueled by partial disclosures mentioning well-known individuals such as former President Donald Trump within these files, no verified evidence has emerged directly connecting them with criminal conduct based on currently unredacted material.
Caution Required When Assessing Unverified Leaked Content
Authorities caution that although technical loopholes permit access to previously hidden data segments,dangers of plucking information sensationalized online claims may lack accuracy or self-reliant verification by credible news sources. Accepting fragmented revelations without context risks spreading misinformation or drawing misleading conclusions.
“Isolating snippets without grasping their full context can easily distort understanding,” warn analysts experienced with complex legal documentation review processes.
The Challenge Of Contextualizing Complex Legal Documents Accurately
Sifting through thousands of pages containing emails, affidavits, financial statements, witness testimonies-and assessing their reliability-requires meticulous attention:
- A circulated lawsuit exhibit alleging illicit videos involving notable figures was later debunked after its creator admitted fabrication;
- Mainstream media outlets often exercise restraint before reporting certain leaked emails due to concerns about authenticity amid Epstein’s history of deception;
- Skepticism remains vital when evaluating explosive claims derived solely from isolated excerpts rather than thorough case reviews;
Navigating The Surge In Public Interest Responsibly Amid Ongoing Revelations
The heightened attention surrounding these disclosures highlights both technological weaknesses within document handling systems as well as society’s demand for transparency regarding powerful individuals indirectly connected through association with Epstein’s network.this underscores why employing an un-redact method , while tempting for uncovering secrets quickly,dangers of plucking information endanger accurate interpretation if done carelessly without full context consideration.
“Attempting interpretation based solely on isolated communications is fraught with risk,” experts emphasize when discussing journalistic caution toward sensational email leaks purportedly implicating major political figures.”
A Call For Thoughtful Analysis Over Sensationalism In Emerging Developments
This unfolding situation serves as a reminder that readers-and researchers alike-must engage critically with leaked materials rather than rushing toward premature judgments founded upon incomplete evidence alone.