Salesforce Cloud Databases Under Siege: cybercriminals Launch Massive Data Extortion Campaign
A New Dark Web Platform Fuels Data Blackmail
A predominantly English-speaking hacker collective has introduced a specialized dark web portal aimed at coercing organizations by threatening to release close to one billion stolen records.these data sets originate from companies that utilize salesforce-hosted cloud databases for managing customer information.
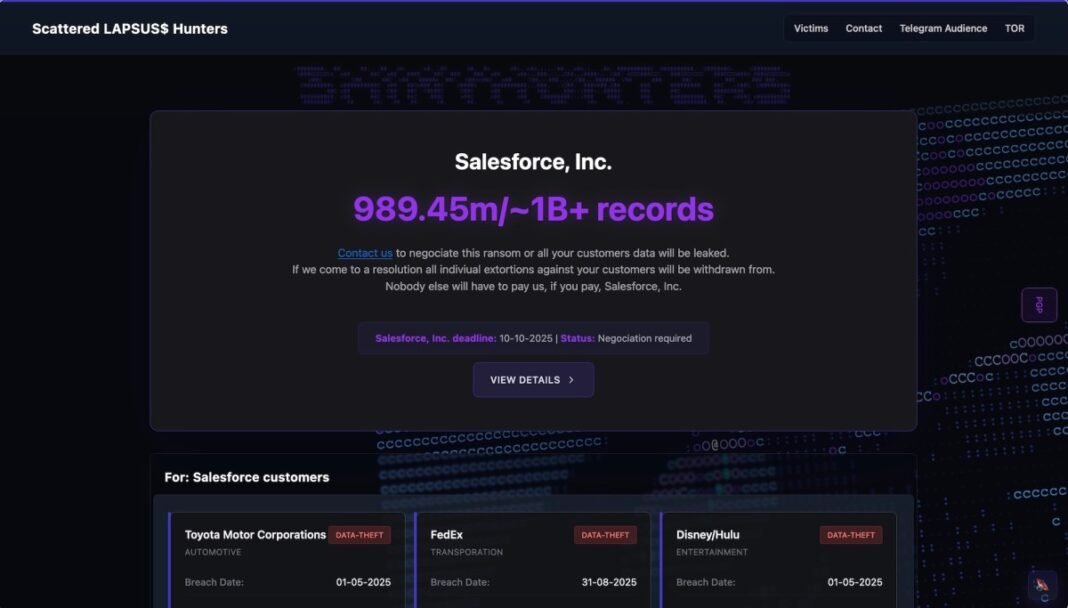
This loosely connected group, previously known under various names such as Lapsus$, Scattered Spider, and ShinyHunters, now operates a site called Scattered LAPSUS$ Hunters. This platform serves as their public hub for leaking data and issuing ransom demands.
Mechanics Behind the Extortion Website
The website explicitly encourages affected businesses to make contact in order to regain control over compromised information and avoid becoming headline news. It highlights stringent verification procedures and guarantees confidential communication channels for negotiation purposes.
“Contact us to restore yoru data control and prevent public disclosure. Don’t become the next major breach story,” the site warns.
Recent High-Impact Breaches Exploiting salesforce Cloud Infrastructure
In recent months, this cybercrime syndicate has breached numerous high-profile organizations by exploiting weaknesses in cloud databases managed through Salesforce platforms. The victims span diverse sectors including insurance, technology, automotive manufacturing, entertainment streaming services, credit reporting agencies, and human resources management systems.
- An international insurance firm serving over 1 million customers confirmed unauthorized access compromising sensitive personal details.
- A leading global technology corporation admitted theft of customer records directly linked to its Salesforce database surroundings.
- A multinational fashion house overseeing luxury brands reported breaches exposing client information stored on cloud servers.
- An airline carrier disclosed that millions of passenger profiles were extracted during an attack targeting its digital infrastructure hosted via Salesforce services.
- A major automobile manufacturer revealed loss of customer personal data following unauthorized access incidents involving third-party cloud providers integrated with their systems.
- A top credit bureau announced hackers accessed millions of consumer profiles through compromised credentials tied to their HR management system provider Workday’s integration with Salesforce databases.
Additional Alleged Victims Named on Leak Portal
The extortion website publicly lists several othre corporations claimed as victims but not yet officially confirmed or responding. Among these are FedEx Logistics Services; Hulu streaming service under Disney’s umbrella; and Toyota Motors Corporation-none have issued statements addressing these allegations so far.
The uncertainty remains weather some targeted companies have settled payments privately since certain hacked entities do not appear on the leak list despite evidence suggesting compromise. Representatives from the hacking group hinted at undisclosed victims without clarifying reasons behind selective disclosure practices featured on their victim roster page.
Explicit Warnings Directed at Salesforce Corporation
The homepage prominently addresses Salesforce, demanding ransom negotiations while threatening widespread exposure of all customers’ sensitive data within its ecosystem if demands remain unmet.the tone suggests ongoing non-engagement between the software giant and threat actors behind this campaign thus far.
Salesforce’s Response Amid Growing Cybersecurity Challenges
A spokesperson for Salesforce acknowledged awareness regarding recent extortion attempts targeting users of its platform but clarified no direct breach or vulnerability exploitation within core infrastructure had been detected:
“Our investigations indicate these threats primarily relate to prior or unverified incidents rather than new compromises affecting our systems,” stated an official company message.
“We continue working closely with impacted clients providing support throughout remediation efforts.”
No further comments were offered beyond confirming active monitoring remains in place against evolving cyber threats leveraging third-party integrations connected with their services worldwide-currently supporting over 170,000 businesses globally according to latest corporate disclosures (2024).
The shift in Ransomware strategies: From encryption Demands To Public Exposure Threats
This trend marks a departure from customary ransomware attacks where criminals encrypt victim files demanding payment for decryption keys. Instead, modern threat actors increasingly rely on double extortion tactics-threatening publication of stolen confidential datasets online if ransoms go unpaid-a method that surged approximately 45% year-over-year according to cybersecurity industry analyses (2024).
The proliferation of publicly accessible leak sites operated by criminal groups once dominated by Russian-speaking hackers now includes younger collectives adopting similar strategies while maintaining anonymity. They amplify pressure through social media leaks or dark web postings designed to maximize reputational damage alongside financial gain potential across industries ranging from healthcare providers safeguarding patient records up through multinational corporations managing vast consumer bases digitally connected via SaaS platforms like Salesforce clouds . Today’s enterprises heavily depend upon these environments for operational continuity and regulatory compliance alike.