Microsoft’s Suspension of Developer Account Threatens VeraCrypt Windows Updates and User Access
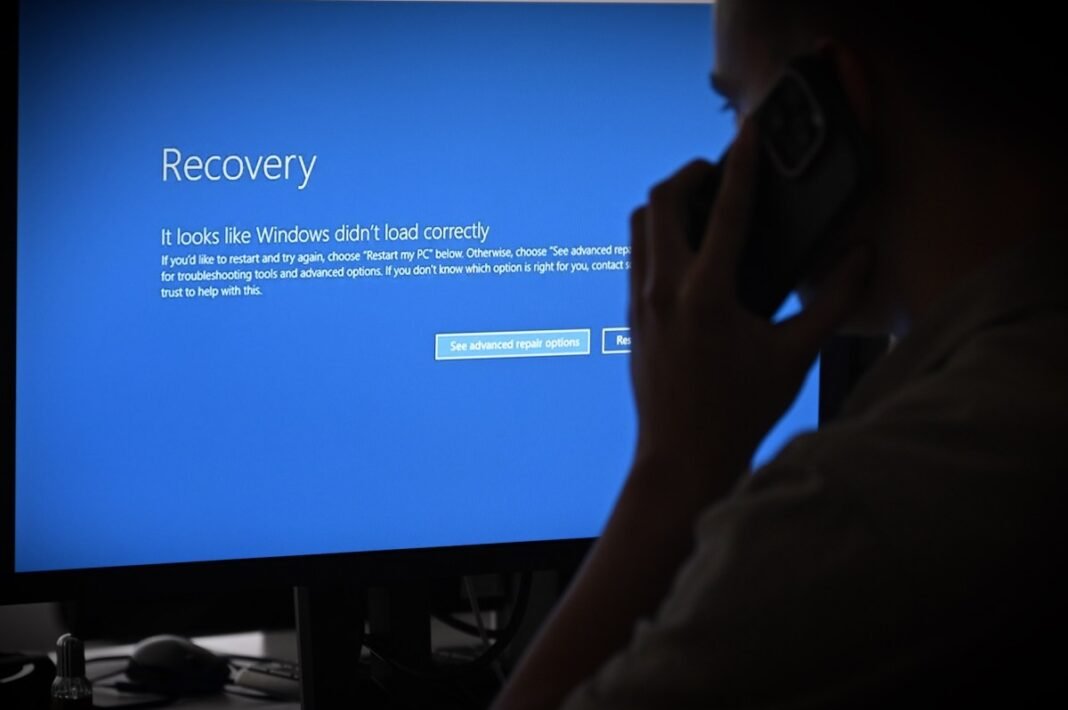
Urgent Consequences for VeraCrypt Users on Windows
The developer behind the trusted encryption software VeraCrypt has disclosed that Microsoft has disabled his developer account, which is essential for distributing updates to Windows users. This suspension risks preventing numerous users who depend on VeraCrypt’s full disk encryption from successfully booting their systems in the near future.
Mounir Idrassi, based in Japan, revealed that Microsoft abruptly terminated his long-standing developer account responsible for signing critical Windows drivers and the bootloader. This action was taken without any prior warning, explanation, or opportunity to appeal. The digital certificate linked to this account is vital because it authenticates software components during system startup.
Boot Failures Coudl Begin by Mid-2026 Without Resolution
If this situation remains unaddressed,devices encrypted with VeraCrypt’s system-wide encryption feature-which safeguards entire operating systems against unauthorized access-may start experiencing boot failures as soon as July 2026. The underlying cause is Microsoft’s planned revocation of the digital certificate authority (CA) used to sign these essential components.
This revocation means that without a valid signature from a recognized CA, Windows will block the execution of the bootloader altogether. Consequently, users could be locked out of their own machines since Idrassi no longer controls his Microsoft developer account and cannot re-sign or update these files with new certificates.
Status Overview Across Platforms and Users
- Windows users: Unable to receive further updates; potential risk of startup failures if full disk encryption remains active.
- Linux and macOS Users: Updates continue unaffected because these platforms do not require Microsoft’s code signing process.
- No Immediate security Threats: Current installations remain operational without known vulnerabilities related to this issue at present.
The Influence of Platform Gatekeepers on Software Distribution
This event highlights how dominant tech corporations exert significant control over third-party applications distributed within their ecosystems. Developers rely heavily on platform-specific accounts and certificates that can be revoked suddenly under opaque policies-posing risks not only for creators but also millions worldwide who trust such tools daily.
A recent parallel involved an independent app creator losing access to their Apple ID after attempting redemption via a suspicious gift card purchase-a problem resolved only after public scrutiny compelled Apple’s intervention. Incidents like these emphasize growing concerns about centralized control over digital identities and software distribution channels in today’s technology surroundings.
The Crucial Role of Code Signing Certificates in Ensuring Software Integrity
A code signing certificate functions as a digital passport confirming both authenticity and integrity before software runs on user devices.For security-critical applications like VeraCrypt-which defends data against sophisticated threats including pre-boot tampering-this verification step is indispensable in preventing malicious actors from injecting harmful code disguised as legitimate updates or drivers.
If developers lose access to certificates or accounts managing them-as Idrassi currently faces-their ability to maintain secure delivery pipelines becomes compromised.This may leave users vulnerable or entirely locked out due to unsigned components being blocked by modern OS security features such as Secure Boot enforced by Microsoft across more than one billion active Windows devices globally.
An Ongoing Challenge for Open Source Encryption Solutions
The most recent version of VeraCrypt released in early 2025 has been downloaded nearly one million times within months-a clear indicator of its widespread use among privacy-conscious individuals amid escalating cybersecurity threats worldwide. However, dependence on proprietary platform controls introduces fragility into open-source projects designed specifically for user autonomy and protection against surveillance or cyberattacks.
“If this problem continues past mid-2026,” warned Idrassi, “it could effectively signal the end of official VeraCrypt support on Windows.”
What Steps Should Affected Users Take Moving Forward?
- No immediate changes needed: existing installations will function normally until certificate revocation occurs next year;
- Avoid activating full disk/system encryption temporarily: To minimize risk until a solution emerges;
- User awareness advised: Monitor official communications closely regarding potential fixes or alternatives;
- Larger community engagement encouraged: Collective advocacy might influence platform providers toward clearer policies supporting vital security tools like VeraCrypt;