Exposing a Sophisticated Phishing Scheme Targeting Signal Users
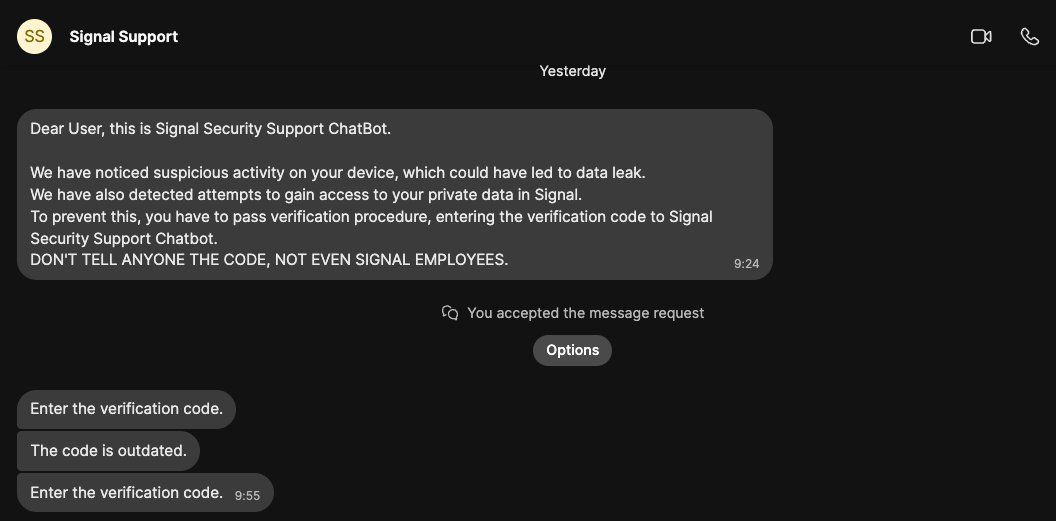
A notable security expert recently encountered an unexpected phishing attempt on his Signal account, a rare reversal of roles for someone who usually investigates spyware rather then being targeted. The fraudulent message warned of suspicious activity adn urged him to verify his identity by submitting a verification code, emphasizing not to share it with anyone-even those claiming to be from Signal’s official team.
Dissecting the Fraudulent Alert
The deceptive notification falsely claimed that unauthorized access attempts had been made on the expert’s private Signal data.It directed him to complete a verification step by sending a code to what was presented as the “Signal Security Support ChatBot.” Recognizing this as an obvious ploy,he chose to analyze the attack rather of falling victim.
Understanding the Larger cyberattack Campaign
this incident is part of an expansive phishing operation targeting tens of thousands of Signal users globally. Attackers impersonate legitimate Signal communications, fabricating urgent security warnings designed to trick victims into linking their accounts with devices controlled by malicious actors. These tactics resemble those employed in recent years by state-sponsored cyber espionage groups.
Multiple national cybersecurity agencies-including those from the United States, United Kingdom, and Netherlands-have issued warnings about similar phishing campaigns attributed to Russian government-backed threat actors. These operations have compromised numerous individuals worldwide, including high-profile political figures across europe and beyond.
The Scope and Techniques Behind This Threat
The researcher identified himself among more than 13,500 confirmed targets in this ongoing campaign. While withholding specific investigative methods for security reasons, he revealed key insights into how these attacks operate:
- The attackers exploit compromised contacts within group chats to rapidly expand their reach-a process described as a “snowball effect.”
- An automated hacking framework known as “ApocalypseZ” facilitates mass targeting with minimal manual effort.
- The control systems and programming languages used are predominantly Russian-based; intercepted victim conversations were reportedly translated into russian during exploitation attempts-strengthening suspicions about state sponsorship.
Real-World Consequences: From Media Professionals To Trusted Contacts
this campaign has also targeted journalists connected with the expert along with close colleagues-demonstrating how attackers leverage social networks once they compromise one individual.this opportunistic strategy significantly increases risks within professional environments where secure communication is essential for confidentiality and trust.
A persistent Threat With Expanding Reach
Months after its discovery, this phishing operation continues unabated; experts estimate that actual victim counts far exceed initial reports. Despite ongoing threats against his network, the researcher remains confident that direct attacks on him will diminish but remains vigilant for any new vulnerabilities (“zero-days”) hackers might expose through such encounters-highlighting his dedication toward proactive cybersecurity research.
Essential Safeguards Against Phishing for Signal Users
If you rely on Signal, activating Registration Lock is crucial-it requires your PIN before anyone can register your phone number on another device.This feature provides vital protection against unauthorized account takeovers triggered through social engineering or sophisticated phishing schemes like those outlined here.





