Widespread DDoS Attack Disrupts Ubuntu and Canonical Online Platforms
A major cyberattack has struck the public infrastructure of Ubuntu, one of the most popular Linux distributions globally, along with it’s parent company canonical. This incident began on Thursday and has caused notable interruptions to essential services used by millions around the world.
Understanding the Nature of the Attack
The disruption stems from a distributed denial-of-service (DDoS) attack, where attackers flood servers with overwhelming traffic volumes to incapacitate them. Despite being a relatively straightforward technique, DDoS attacks remain among the most effective methods for causing widespread service outages.
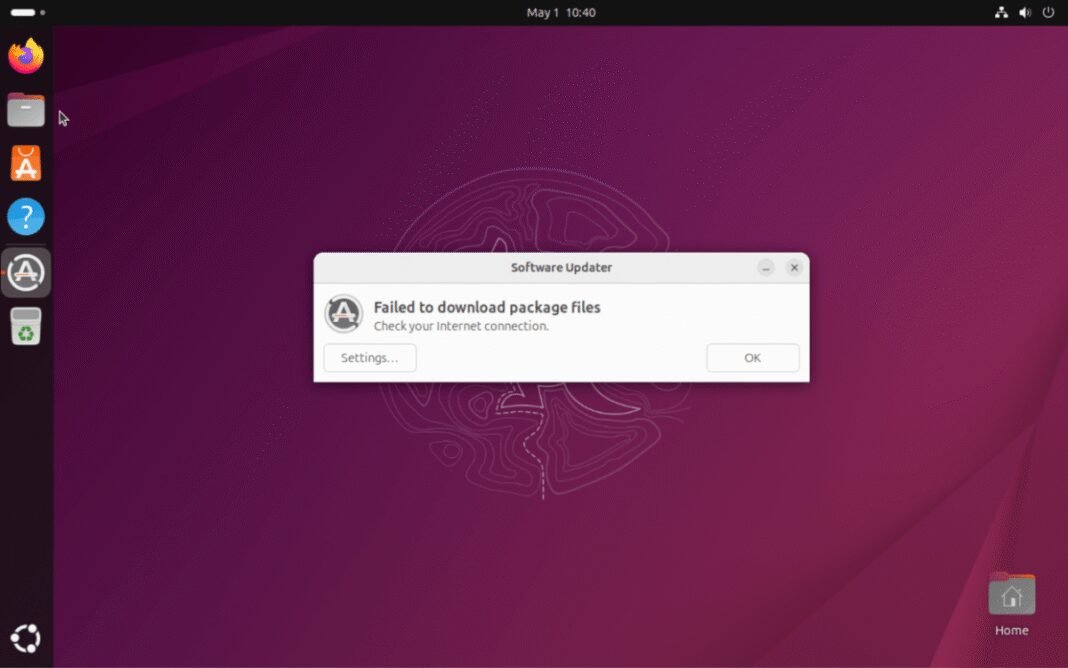
Canonical’s teams have confirmed that this ongoing assault is impacting several critical components such as Ubuntu’s security API and multiple official websites managed by canonical. Users attempting software updates or installations have faced repeated failures due to these service interruptions.
Impact Duration and User Experience
The outage has lasted close to 20 hours, severely affecting users who rely on timely system updates for security patches and functionality improvements. Routine maintenance tasks or upgrades during this period have largely been unsuccessful, underscoring how disruptive this event has been for both individual users and organizations dependent on Ubuntu systems.
Identifying Those Responsible for the Incident
A hacktivist collective calling themselves Islamic Cyber Resistance in Iraq 313 Team claimed responsibility through their Telegram channel. They revealed that they employed a commercial DDoS-for-hire service named Beamed to orchestrate this large-scale attack.
DDoS-for-hire platforms-also known as booters or stressers-allow individuals without deep technical knowledge to launch powerful attacks by renting access to extensive botnets capable of generating enormous amounts of junk traffic. In this case,Beamed reportedly supports assaults exceeding 3.5 terabits per second (Tbps), which is about half as intense as last year’s record-breaking 7.3 Tbps DDoS, one of the largest ever recorded worldwide.
The Global Fight Against DDoS-for-Hire Services
- International law enforcement agencies such as Europol and FBI have long targeted these illicit services through domain seizures and arrests aimed at dismantling their operations.
- The FBI recently escalated efforts against booter sites responsible for numerous high-profile disruptions across various industries including finance,healthcare,and government sectors.
- This ongoing battle highlights persistent challenges in combating decentralized cybercrime infrastructures fueled by commoditized tools readily available in underground markets worldwide.
- Despite crackdowns, new DDoS-for-hire platforms continue emerging due to low barriers preventing entry into this illegal ecosystem.
Evolving Risks Within Open source Ecosystems Like Ubuntu
This event exposes vulnerabilities even within open source communities often perceived as more secure because of openness but remain attractive targets given their vast user base spanning governments, enterprises, educational institutions, and individual enthusiasts alike.
For example,Ubuntu’s widespread adoption in cloud environments-including over 40% usage share among public cloud Linux instances-makes it an especially valuable target for attackers aiming at foundational technology providers supporting global digital infrastructure.
“The scale and persistence observed here highlight why organizations backing open source projects must invest heavily in resilient infrastructure designed specifically to withstand volumetric attacks,” cybersecurity experts emphasize following similar recent disruptions affecting other major platforms worldwide.”
User Recommendations During Service Interruptions
- Avoid updating systems: Until official confirmation signals restoration of normal operations avoid installing or updating packages which may fail mid-process potentially causing data corruption issues.
- Mimic vigilance via official channels: Follow verified announcements from Canonical closely regarding progress toward resolution timelines or choice update procedures if provided during outages.
- Create offline backups:If feasible maintain local snapshots before applying changes once stability returns ensuring minimal downtime impact moving forward amid unpredictable disruptions like these events cause regularly now globally .
Towards Stronger Defenses Against Large-Scale Cyberattacks
This incident serves as a stark reminder about growing sophistication among threat actors leveraging rented botnets capable not only disrupting commercial enterprises but also critical technology providers integral across global digital ecosystems.
With cloud adoption rates surpassing 80% among Fortune 500 companies alone,the urgency intensifies around deploying robust defense mechanisms tailored specifically against volumetric assaults targeting essential software distribution networks like those operated by Canonical.
Emerging mitigation strategies include AI-powered anomaly detection combined with advanced traffic filtering alongside enhanced collaboration between private sector cybersecurity teams working jointly with governmental task forces focused on preemptive identification & takedown operations targeting booter marketplaces fueling such campaigns.