Intellexa’s Predator Spyware: Exposing Direct Remote Access to Government Surveillance Networks
Revealing the Depths of Spyware operations
Recent disclosures have uncovered that Intellexa, the company behind the Predator spyware, maintained direct remote access to surveillance systems operated by some government clients. This access allowed Intellexa personnel to view highly sensitive personal data extracted from devices infected with their spyware.
The revelations stem from an extensive investigation involving leaked internal documents, promotional content, and training materials sourced from Intellexa’s own files. These findings were corroborated by a coalition of investigative journalists and human rights organizations.
utilizing Common Remote Desktop Software for System control
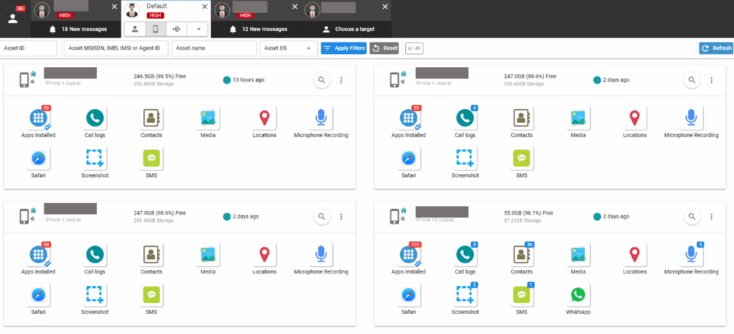
A particularly concerning aspect is that Intellexa employees reportedly leveraged TeamViewer-a widely used remote desktop application-to connect directly into customer surveillance platforms.A leaked instructional video illustrates this process, revealing privileged sections within the Predator spyware interface such as control panels and databases containing intercepted images, messages, and other private details harvested from compromised smartphones.
Real-Time Infection Attempts Captured in leaked Videos
The footage also appears to document live infection attempts targeting real individuals. One segment includes detailed metadata such as infection URLs and IP addresses linked to targets in kazakhstan alongside device software versions-indicating active exploitation rather than staged demonstrations.
Industry Standards Compared with Actual Practices
Leading spyware vendors like NSO Group or Hacking Team have long maintained they do not retain post-sale access to their customers’ intercepted data or systems. This policy aims both to reduce legal liability for misuse by clients and reassure governments concerned about foreign companies accessing confidential investigations involving dissidents or journalists.
This makes Intellexa’s apparent practice highly unusual within the sector. Paolo Lezzi, CEO of Memento Labs-a competing firm-expressed doubt that unrestricted remote access is standard industry protocol. He noted government agencies typically reject arrangements granting external parties unfettered entry into their surveillance operations.
Lezzi suggested some leaked materials might depict controlled demonstration environments rather than live systems but acknowledged scenarios where temporary supervised technical support via tools like TeamViewer could be permitted under strict oversight conditions.
Amnesty International Confirms Access Was on Active Systems
Donncha Ó Cearbhaill from Amnesty International’s security lab verified that during a training session shown in the leaks one participant questioned weather it was a demo surroundings; an instructor explicitly confirmed it was connected to a live customer system. This admission intensifies concerns over privacy violations stemming not only from state-sponsored spying but also potential exposure through third-party company employees wielding broad system privileges.
“Targets face dual threats: intrusion by state actors deploying sophisticated malware plus unauthorized scrutiny by foreign corporate staff entrusted with managing these tools.”
The Privacy Risks for Those Under Surveillance
The fact that company personnel could observe who was being monitored raises serious questions about safeguards protecting victims’ most intimate details-from communication contents to location tracking-potentially exposing them beyond what has been publicly recognized until now.
A Controversial Leader Behind Intellexa: Tal Dilian
- Tal Dilian-the founder associated with Intellexa-is infamous within cybersecurity circles for his overt approach operating in this clandestine industry without much discretion compared with peers who often maintain low profiles due to legal sensitivities surrounding espionage technologies worldwide;
- Dilian has faced U.S.-imposed sanctions barring American entities from commercial dealings following allegations his products targeted U.S.-based officials and journalists unlawfully during 2024-2025 campaigns against civil society figures globally;
- This marked one of the earliest instances where sanctions targeted an individual rather than just companies involved in offensive cyber tool sales;
- Dilian denies any wrongdoing while accusing media coverage of politically motivated efforts aimed at undermining his business interests abroad;
- The controversy highlights ongoing tensions between national security priorities versus human rights protections amid expanding digital surveillance capabilities worldwide;
- An estimated 50 countries currently deploy commercial-grade spyware solutions similar in scope though varying widely regarding oversight mechanisms implemented internally or externally;
- This case underscores how insufficient transparency can exacerbate abuses when powerful technology falls into hands lacking accountability frameworks aligned with international law standards;
The Expanding Market and Risks of Commercial Spyware Today
The global trade in government-grade hacking software continues its rapid expansion despite growing ethical concerns; recent estimates place annual revenues above $6 billion across numerous firms supplying covert smartphone infiltration tools worldwide.
- A prominent example outside this case involves Pegasus malware developed by NSO Group which has repeatedly been implicated since 2016 in targeting activists across multiple continents;
- Civil liberties groups warn unchecked proliferation threatens democratic institutions given how easily attackers gain persistent control over mobile devices containing personal secrets including health records and financial transactions;
- Lax regulatory frameworks combined with opaque sales practices fuel fears intelligence services may exploit vulnerabilities without sufficient judicial oversight leading innocent people caught up inadvertently becoming collateral damage during espionage campaigns;
Pushing Toward Enhanced Oversight?
This incident spotlights urgent calls for stronger governance models regulating export controls on offensive cyber capabilities alongside rigorous auditing procedures ensuring compliance among vendors servicing state actors globally-especially those operating beyond traditional legal jurisdictions yet impacting fundamental rights wherever digital footprints exist today.





