Assessing the Security Framework of XChat: X’s Latest encrypted Messaging Solution
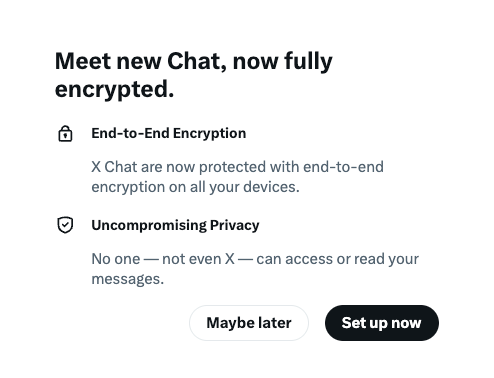
X, previously known as Twitter, has launched a new encrypted messaging service named “XChat” or simply “chat.” This feature aims to deliver end-to-end encryption, ensuring that only the communicating parties can access the message content.Ideally, this means that even X itself should be unable to view private conversations exchanged thru this platform.
Understanding XChat’s Encryption Mechanism and Emerging Concerns
To activate xchat, users must create a four-digit PIN which encrypts their private cryptographic key stored on X’s servers.This private key is essential for decrypting incoming messages and works in tandem with a public key used by senders to encrypt outgoing communications.
This server-based storage of private keys diverges significantly from industry leaders like Signal, where keys remain exclusively on user devices. Storing sensitive cryptographic material remotely introduces notable security vulnerabilities that experts warn against.
Potential Dangers Linked to Server-Hosted Private Keys
Security professionals emphasize that without deployment of hardware security modules (HSMs)-specialized devices designed to protect cryptographic keys from extraction or tampering-even insiders at the company could potentially access these keys. HSMs act as fortified vaults preventing unauthorized use or theft of encryption credentials.
An engineer affiliated with X has asserted that HSM technology is employed; though, no publicly verifiable evidence supports this claim yet. In absence of transparent proof regarding such safeguards, reliance on trust rather than demonstrable security remains problematic for privacy advocates.
The Risk of Insider Threats and Man-in-the-Middle exploits
X openly admits in its documentation that current implementation may allow malicious insiders-or even corporate actors-to intercept encrypted chats through adversary-in-the-middle (AITM) attacks. Such vulnerabilities fundamentally compromise end-to-end encryption by enabling third parties within the system infrastructure to decrypt message contents undetected.
“Since users receive public keys directly from X during conversations without independent verification methods like key fingerprint checks or out-of-band confirmation, it becomes nearly impractical for them to detect if those keys have been swapped,” explains an expert analyzing these risks.
The Impact of Closed-Source Code on User Confidence
Unlike open-source platforms such as Signal-which publish their entire encryption protocols for community scrutiny-XChat currently operates with proprietary code inaccessible for external review. Even though plans exist to release technical whitepapers and some open-source components later in the year, until then there is no way for independent auditors or privacy specialists to validate claims about its security architecture thoroughly.
The Absence of Perfect Forward Secrecy: A Notable Security Gap
A critical omission in XChat’s design is perfect forward secrecy (PFS). PFS ensures each message session uses unique ephemeral encryption keys so compromising one does not jeopardize past communications. Without PFS-a feature standard even among many less robust apps-all previous messages become vulnerable if an attacker ever obtains a user’s private key at any point in time.
Cautionary Perspectives From Cryptography experts
- Matthew Garrett: Highlights that assuming all involved parties are fully trustworthy-a rare scenario-the current architecture still falls short compared with industry benchmarks like Signal due mainly to server-side storage risks and lack of forward secrecy.
“Even initial trust cannot guarantee ongoing protection given potential shifts in corporate policies or personnel.” - Matthew Green:, professor specializing in cryptography,
“Until subjected to rigorous external audits by reputable experts familiar with secure messaging protocols, I would consider this service no more secure than unencrypted direct messaging.”
A Contemporary Comparison: Messaging privacy Models Across Platforms
The contrast between Signal’s device-centric approach-where all sensitive data remains local-and other popular services illustrates how architectural choices shape global user privacy outcomes today. For instance,WhatsApp offers technically similar end-to-end encryption but faced backlash over metadata collection practices raising surveillance concerns worldwide despite its encrypted core functionality. Meanwhile newer platforms emphasizing openness via open-source advancement continue gaining traction among privacy-conscious communities amid escalating digital monitoring threats globally.
Final Thoughts: Exercise Prudence When Using XChat Today
XChat marks an aspiring attempt at enhancing communication privacy within one of social media’s largest ecosystems; however several unresolved issues currently prevent it from meeting established standards set by leading encrypted messengers such as Signal. until full transparency about implementation details emerges alongside robust protections-including hardware-backed key management and integration of perfect forward secrecy-and until independent audits confirm these claims beyond doubt-users should remain cautious about entrusting highly sensitive information solely through this new feature.





